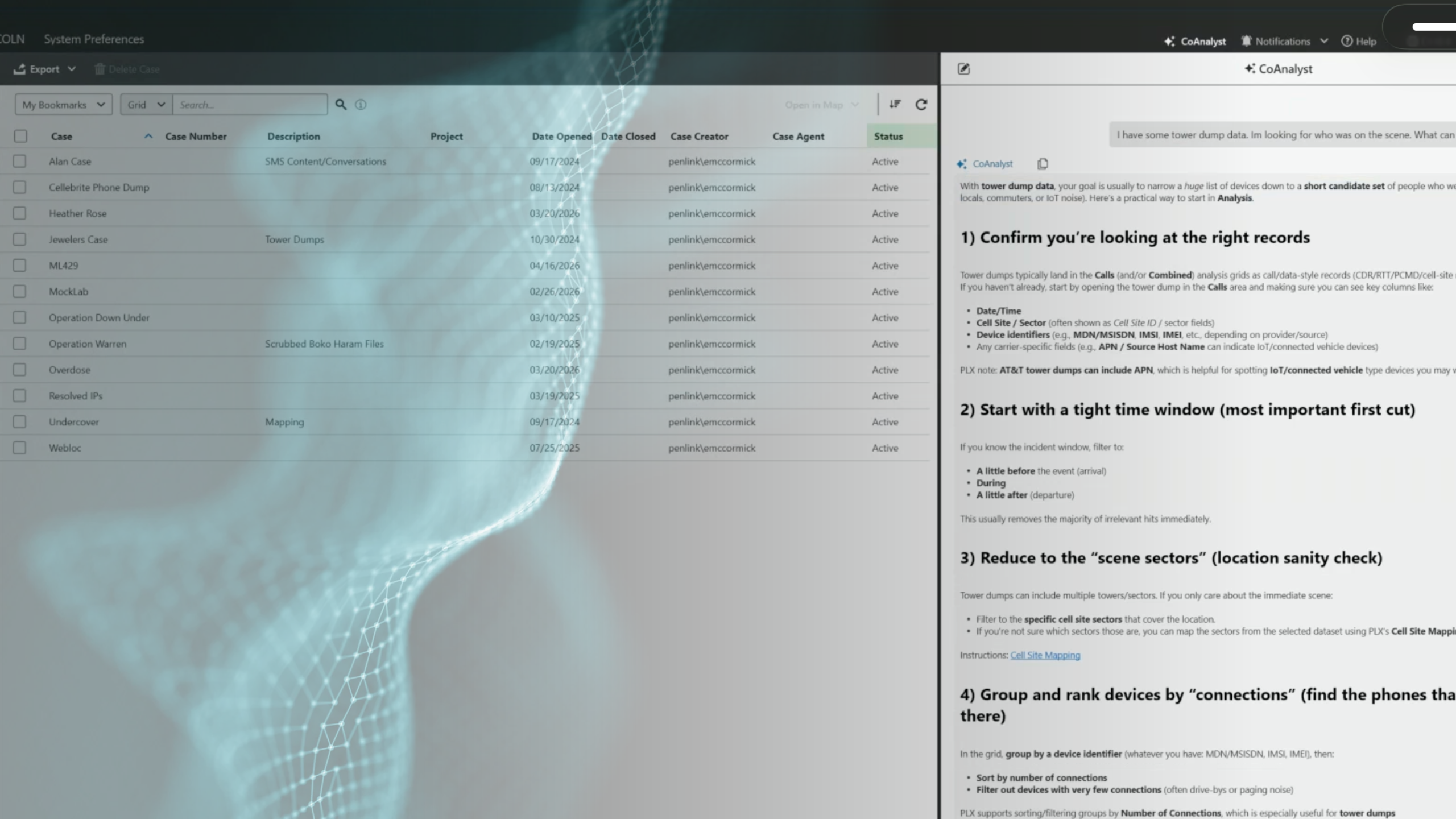
CoAnalyst for PLX: Turning Digital Evidence into Decisive Action
Investigators face more data than ever. CoAnalyst for PLX brings generative AI directly into PLX, helping agencies move faster from raw data to actionable insight.
Cyber threats do not wait for agencies to catch up. Adversaries move quickly, share tactics openly in dark web forums, and exploit gaps before most organizations know those gaps exist. Open source intelligence has become one of the most practical tools available for closing that distance, not after an incident, but before one takes shape.
Penlink recently appeared on The OSINT Edge, a program broadcast on Fed Gov Today, to discuss how OSINT is reshaping the way agencies approach cyber threat detection. The conversation covered where the field is heading, what analysts need to work effectively, and why the combination of technology and human judgment matters more than ever. Watch the full segment above.
For most of the past two decades, cybersecurity operated on a reactive model. An incident occurred, analysts investigated, and agencies responded. That model is no longer sufficient. Threat actors are organized, persistent, and increasingly vocal about their intentions in spaces that are publicly accessible to anyone with the right tools.
The commercial sector recognized this early. Significant investment over the past ten-plus years has produced platforms capable of monitoring open source intelligence at scale, scanning for indicators of compromise, tracking external risk, and surfacing relevant signals before they become active threats. That capability has matured considerably and is now within reach of government agencies that need it most.
The result is a meaningful shift in how analysts spend their time. Instead of triaging incidents after the fact, teams can now focus on anticipating attack vectors and acting on intelligence before damage occurs. That is a significant change in operational posture, and it is driven by the availability of open source data.
One of the more important reframes in modern cyber intelligence is how analysts think about the dark web. It is often discussed as a place where threats originate. That is true. However, it is also a place where those threats are openly discussed, coordinated, and telegraphed well in advance of any actual attack.
Threat actors share tactics, tools, and targets in these environments. They recruit, advertise, and communicate in ways that create a visible record. For analysts with the right access and the right tools, that record is actionable intelligence. The question is not whether the information exists. The question is whether agencies have the capability to find it and act on it in time.
This is where structured data analysis becomes operationally relevant. Volume alone is not the challenge. The challenge is identifying what matters within that volume, quickly enough to be useful.
The volume of data flowing through open sources today is not manageable through manual review alone. AI and automation are now core parts of how effective cyber threat intelligence programs operate. Platforms can monitor activity across multiple sources simultaneously, identify patterns, and generate alerts based on specific criteria, allowing analysts to focus attention where it matters most.
However, technology does not replace the analyst. It changes what the analyst is asked to do. Processing volume becomes the machine’s job. Interpreting context, validating findings, and making decisions that require judgment remain the analyst’s responsibility. That balance is not a limitation of current technology. It is the right division of labor.
For law enforcement and defense teams building or scaling a cyber intelligence program, this means the investment in tooling needs to be matched by investment in experienced analysts who know how to work with the output. One without the other leaves significant capability on the table.
Open source intelligence is not a future capability. For agencies willing to build the right foundations, it is a present-day advantage.
Penlink’s platform brings OSINT and data analytics together in one investigative workflow. Request a demo to see what that looks like in practice.